- Security
- 25 May 2014 at 14:59 UTC
-

A new virus called "Crypto Locker" appeared on the web.
Here is an overview of it.
This new ransomware is very dangerous because it encrypts your files and if you do not pay the ransom before the deadline, the program will format your hard drive.
Apparently the program was performing the formatting of data at the end of the period if the fine was not paid (Attention : Pay the fine is useless. the hacker will not send you the unlock code).
Warning : pay the ransom is useless. Which seems logical. The goal of this type of program is to blame the user with illegal actions that supposedly committed and thus earn money illegally.
The virus is compatible with Windows and Mac. Like what, even on the Mac, you can get viruses.
The virus would come as an attachment (zip or pdf format) by e-mail or through suspects Internet websites.
This virus encrypts your data with a key RSA-2048. Let me tell you that even brute-force, it will be impossible to find private decryption key corresponding to the public key generated for your computer.
As indicated above, the ransomware Crypto Locker will format your computer at the end of the period. In other words, the program will permanently erase your entire hard drive.
Since we do not know if it's a classic format or a more sophisticated formatting, we can not assure you that the data recovery programs work.
Now that you know more about this ransomware, here's how to protect yourself.
- Update your computer (OS)
- Update your programs
- Update your firewall and antivirus
- Make antivirus and antimalware scans
- Purchase and install Malwarebytes Anti-Malware Premium
- Protect yourself from security vulnerabilities with Malwarebytes Anti-Exploit
- Pay attention to what you do on the Internet
- Make backups of your data on an external hard drive
- Block the execution of exe file in %AppData% folder
1. Update your computer (OS)
On Windows, you can simply use Windows Update to automatically download and install updates for Windows (including its security updates for correcting the security vulnerabilities that are found in Windows.)
Note : If you are still running Windows XP despite the end of its support by Microsoft. Know that your computer is vulnerable to attacks that ransomware.
Under Mac, you just go to the Apple App Store.
2. Update your programs
You can not say it enough : keep your programs up to date.
Why you ask? For several reasons :
- the principal : Each program contains security flaws and they are corrected progressively by their manufacturer. Thus, a program updated contains fewer security vulnerabilities and virus therefore has less chance to run and mess up your computer
- Second : If you keep your programs up to date, you can avoid compatibility problems that would occur one day or the other.
- Then we also include : stability programs and new features but we digress from the subject.
To update your programs, you have several options :
- Use the check for updates function of your programs (if this function exists)
- Download the latest version of each program on the manufacturer's website (or clubic.com which is a very known and therefore reliable download site legal)
3. Update your firewall and antivirus
To protect against the latest viruses, spywares, ransomwares and other malwares, it's very important that your anti-virus is up to date.
When we talk about "antivirus updated", we are talking about the version of your anti-virus and the version of the virus database (also called : VPS virus database by Avast). It's obvious that cracked antivirus should be avoided.
4. Make antivirus and antimalware scans
For the same reasons than the update programs, we recommend you to perform antivirus and anti-malware scans with : Rogue Killer, Malwarebytes Anti-Malware (free or paid) and then with your antivirus.
Warning : don't run Rogue Killer and Malwarebytes Anti-Malware at the same time. They are scanning tools that can be installed and used in addition to your anti-virus programs but these two don't like being launched simultaneously.
The reasons why we recommend that you perform these scans are simple :
If your computer is infected with a virus or trojan or worse : a bot. Your computer may automatically receive this ransomware without your consent (the principle of a virus, in fact). It's even possible you propagate the ransomware unknowingly and therefore it also would put your family and your professional relationships in danger.
5. Purchase and install Malwarebytes Anti-Malware Premium
We don't usually propose to pay special software (or so we try to provide free alternatives when possible), but this time, the purchase of this security program will protect you from this ransomware and therefore it may prevent you from losing your data (because, remember it, your data will be encrypted by this virus and it will be impossible to decrypt your data without the private key stored on the pirate's server.).
The paid version of the program can protect yourself from this virus with its real-time protection that is not present in the free version.
Note : If you have already purchased Malwarebytes Anti-Malware Pro (the paid version 1), we recommend that you install the new version (version 2 : Premium). Your serial number is the same for the new version of Malwarebytes Anti-Malware.
As you can see, the real-time protection for the paid version of Malwarebytes Anti-Malware detects this ransomware and prevent its installation.
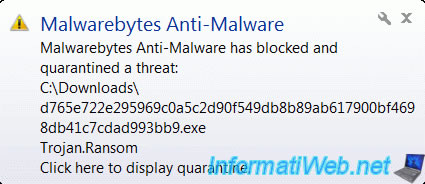
Source : forums.malwarebytes.org
6. Protect yourself from security vulnerabilities with Malwarebytes Anti-Exploit
Now that your operating system (Windows or Mac) and your programs are up to date, we will protect your web browsers (Mozilla Firefox, Google Chrome, ...) as well as other programs that Microsoft office suite through Malwarebytes Anti-Exploit program is the same manufacturer as the anti-malware.
As indicated by the name of the program, it will allow you to protect yourself from security vulnerabilities of these programs. Thus, when a malicious website will attempt to install a virus on your computer, Malwarebytes Anti-Exploit prevent it from install it and you can avoid getting this ransomware on your computer. For the protection of your web browser, this program is able to block exploits using plugins used by your browser as Adobe Flash, Microsoft Silverlight or Java.
7. Pay attention to what you do on the Internet
All IT professionals and computer stores will tell you : the best antivirus is you.
Indeed, in most cases, it is possible to avoid downloading these viruses.
Here are some examples :
- You receive a suspicious message. An English message from a sender that is unknown to you. Or a response (RE : something) in an email than you have not sent. It's obviously spam and / or a message that contains a virus attached. Reminder : The "Crypto Locker" also would come by mail to zip or pdf format.
- A website display a message like "Your PC is infected. Download this program to remove the virus." Or "xx errors found on your computer". This kind of advertising will offer you to download a program that will delete anything that will crash your computer and install one or more viruses on your computer. Sometimes, some of these programs look like a antivirus. These are obviously fake antivirus.
8. Make backups of your data on an external hard drive
Indeed, once encrypted, your data will be lost for several reasons :
- Find private key by "brute-force" mode isn't realistic given the length of the encryption key.
- Paying the ransom will not help because the attacker doesn't send you the private key. It would not do them any good and they could be arrested for nothing.
- No antivirus program or another can decrypt your data without the key. It's impossible and it isn't their goal either.
The solution is to make backups of your data on an external hard drive. Thus, if the virus arrives one day on your computer, you will have a copy of your data, so you will lose nothing.
Note: Obviously, he advised not to leave your external hard drive plugged in all the time. If it is still connected when the virus arrives, the virus may infect your backups.
If you are an individual, you can use "Cobian Backup pour Windows".
If you are a professional, you can use the Acronis solutions like "Acronis Backup & Recovery" or "Acronis True Image".
9. Block the execution of exe file in %AppData% folder
Finally, you can also prohibit the execution of executable programs (.exe) in "%AppData%" folder and in its subfolders.
Note : This ransomware is still in this folder or folder in this folder with a random name.
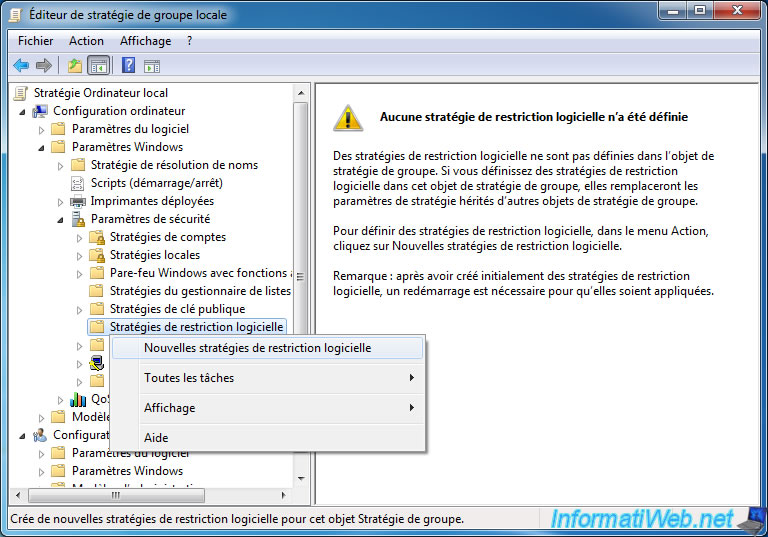
To perform this restriction, launch "gpedit.msc" program through the start menu -> Run or through the start menu and type "gpedit.msc" in the search box.
A window named "Local Group Policy Editor" will be displayed. In this window, go to : Computer Configuration -> Windows Settings -> Security Settings.
Then, right-click on "Software Restriction Policies" and click "New Software Restriction Policies".
Note : For more information about software restriction, refer to the Microsoft website.
Then, go to "Supplemental Rules". Right click on the right side and click on "New rule path".
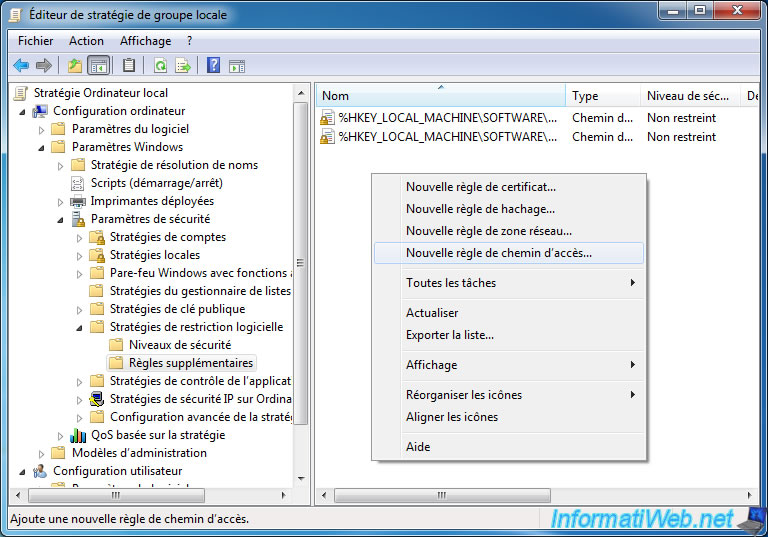
In this window, specify the following information :
- Path : %AppData%\*.exe
- Security Level : Not permitted (which will block the execution of the program regardless of the rights of the user) or rejected on Windows XP.
- Description : Don't allow executable files from the %AppData% folder.
Then, do the same thing to block the exe present in a sub-folder in the %AppData% folder :
- Path : %AppData%\*\*.exe
- Security Level : Not permitted or denied on Windows XP.
- Description : Don't allow executable files from a subfolder of %AppData% folder. The sub-sub-folders are not affected by this restriction.

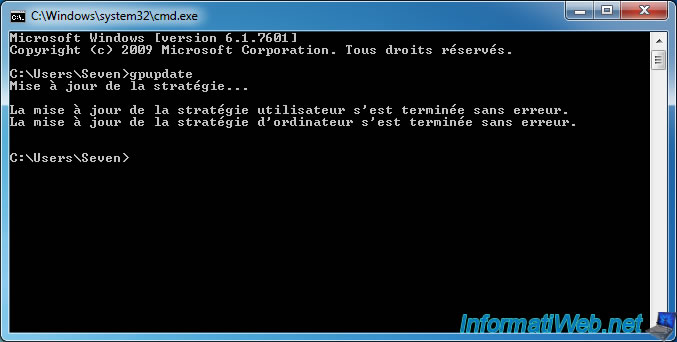
Finally, you must apply the following rules by running "gpupdate" in the command prompt (cmd.exe) and then restart your computer.
Maintenant, accédez au dossier "%AppData%", copiez un programme portable à l'intérieur (par exemple, le bloc-notes : C:\Windows\notepad.exe) et tentez de le lancer.
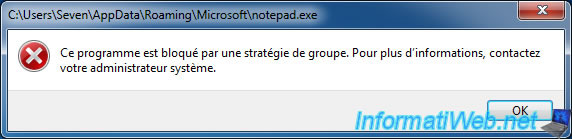
Si tout se passe bien, un message d'erreur devrait s'afficher et le programme ne se lancera pas.
Now, go to "%AppData%" folder, copy a program (for exemple, Notepad : C:\Windows\notepad.exe) inside this folder and try to run it.
If all goes well, an error message should be displayed and the program will not launch.
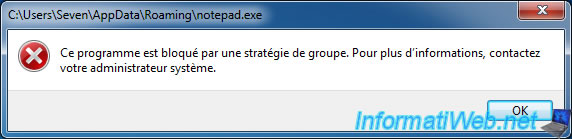
Try running the same program in one of the folders in the "%AppData%" folder.
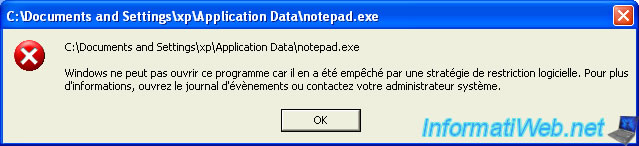
And to prove the manipulation also work on Windows XP, here's the error message.
Share this tutorial
To see also
-
Security 2/19/2016
Avast Free Antivirus - The best antivirus
-
Security 6/13/2014
DiskCryptor - Encrypt your USB key
-
Security 3/6/2016
Malwarebytes Anti-Exploit - Protection against zero-day
-

Security 6/5/2016
Secure your Internet connection (VPN)

You must be logged in to post a comment